Scan a Single Host or an IP Address. Scan a Single IP Address: $ nmap 192.168.1.1.
With the ubiquity of mobile devices and cheap commoditynetworking equipment, companies are increasingly finding thatemployees are extending their networks in undesirable ways. Among themost dangerous devices are 802.11 wireless access points (WAPs). Users mayinstall a $20 WAP in their cubicle so they can work from the breakroom, without realizing (or caring) that they just opened theprotected corporate network to potential attackers in the parking lotor nearby buildings.
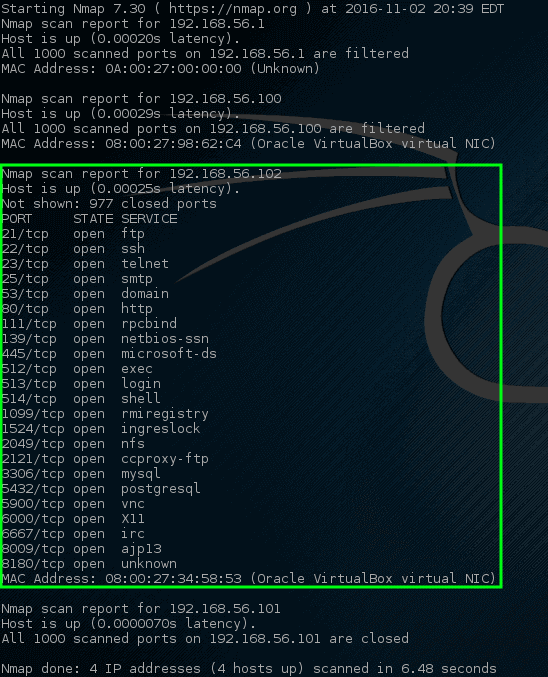
- I notice that nmap -sn is no longer provide the MAC address for remote host as discussed in Can I use nmap to discover IPs and mac addresses? I would like to get something like netdiscover output. Just IP & MAC Address only. Nmap version 7.80. Wolf@linux:$ nmap -V Nmap version 7.80 ( ) Platform: x8664-pc-linux-gnu e.g.
- Nmap is a free and open-source network, especially for discovering the network, including security auditing. Nmap provides support to the professionals of cybersecurity, system, and network administrators. Nmap is suitable for the basic operating systems such as Linux, MAC OS X, and windows. In this article, how to perform a UDP scan using Nmap tool in Kali Linux 2020 is explained.
- I notice that nmap -sn is no longer provide the MAC address for remote host as discussed in Can I use nmap to discover IPs and mac addresses? I would like to get something like netdiscover output. Just IP & MAC Address only. Nmap version 7.80. Wolf@linux:$ nmap -V Nmap version 7.80 ( ) Platform: x8664-pc-linux-gnu e.g.
- Nmap is a free and open-source network, especially for discovering the network, including security auditing. Nmap provides support to the professionals of cybersecurity, system, and network administrators. Nmap is suitable for the basic operating systems such as Linux, MAC OS X, and windows. In this article, how to perform a UDP scan using Nmap tool in Kali Linux 2020 is explained.
Some WAP installations are even worse than those installed by naive users.Breaching a building's security is much riskier for an attacker thanaccessing corporate data from far away through a network. It carries the risk ofbeing arrested on the spot. So attackers have been known to installcompact WAPs so they can then intrude on the network at will from therelative safety of a car down the street. A WAP taped under a desk orotherwise hidden is unlikely to be noticed for a while.
While the focus of this solution is finding WAPs, the samestrategy can be used to find just about anything. You might need tolocate all Cisco routers to apply a new patch or Solaris boxes todetermine whether you have enough systems to warrant paying forsupport. Download video player for mac.
One way to find unauthorized wireless devices is to sweep thearea with a wireless sniffer such as Kismetor NetStumbler.Anotherapproach is to scan the wired side with Nmap. Not surprisingly, thissolution focuses exclusively on the latter approach. Each techniquecan miss certain WAPs, so the best approach is to do both and merge the results.
Latest versionReleased:
This is a python class to use nmap and access scan results from python3
Project description
python-nmap
python-nmap is a python library which helps in using nmap port scanner.
It allows to easilly manipulate nmap scan results and will be a perfect
tool for systems administrators who want to automatize scanning task
and reports. It also supports nmap script outputs.
Typical usage looks like::
#!/usr/bin/env python
import nmap # import nmap.py module
nm = nmap.PortScanner() # instantiate nmap.PortScanner object
nm.scan('127.0.0.1', '22-443') # scan host 127.0.0.1, ports from 22 to 443
nm.command_line() # get command line used for the scan : nmap -oX - -p 22-443 127.0.0.1
nm.scaninfo() # get nmap scan informations {'tcp': {'services': '22-443', 'method': 'connect'}}
nm.all_hosts() # get all hosts that were scanned
nm['127.0.0.1'].hostname() # get one hostname for host 127.0.0.1, usualy the user record
nm['127.0.0.1'].hostnames() # get list of hostnames for host 127.0.0.1 as a list of dict
# [{'name':'hostname1', 'type':'PTR'}, {'name':'hostname2', 'type':'user'}]
nm['127.0.0.1'].hostname() # get hostname for host 127.0.0.1
nm['127.0.0.1'].state() # get state of host 127.0.0.1 (up|down|unknown|skipped)
nm['127.0.0.1'].all_protocols() # get all scanned protocols ['tcp', 'udp'] in (ip|tcp|udp|sctp)
nm['127.0.0.1']['tcp'].keys() # get all ports for tcp protocol
nm['127.0.0.1'].all_tcp() # get all ports for tcp protocol (sorted version)
nm['127.0.0.1'].all_udp() # get all ports for udp protocol (sorted version)
nm['127.0.0.1'].all_ip() # get all ports for ip protocol (sorted version)
nm['127.0.0.1'].all_sctp() # get all ports for sctp protocol (sorted version)
nm['127.0.0.1'].has_tcp(22) # is there any information for port 22/tcp on host 127.0.0.1
nm['127.0.0.1']['tcp'][22] # get infos about port 22 in tcp on host 127.0.0.1
nm['127.0.0.1'].tcp(22) # get infos about port 22 in tcp on host 127.0.0.1
nm['127.0.0.1']['tcp'][22]['state'] # get state of port 22/tcp on host 127.0.0.1 (open
# a more usefull example :
for host in nm.all_hosts():
print('----------------------------------------------------')
print('Host : %s (%s)' % (host, nm[host].hostname()))
print('State : %s' % nm[host].state())
for proto in nm[host].all_protocols():
print('----------')
print('Protocol : %s' % proto)
lport = nm[host][proto].keys()
lport.sort()
for port in lport:
print('port : %ststate : %s' % (port, nm[host][proto][port]['state']))
print('----------------------------------------------------')
# print result as CSV
print(nm.csv())
print('----------------------------------------------------')
# If you want to do a pingsweep on network 192.168.1.0/24:
nm.scan(hosts='192.168.1.0/24', arguments='-n -sP -PE -PA21,23,80,3389')
hosts_list = [(x, nm[x]['status']['state']) for x in nm.all_hosts()]
for host, status in hosts_list:
print('{0}:{1}'.format(host, status))
print '----------------------------------------------------'
# Asynchronous usage of PortScannerAsync
nma = nmap.PortScannerAsync()
def callback_result(host, scan_result):
print '------------------'
print host, scan_result
nma.scan(hosts='192.168.1.0/30', arguments='-sP', callback=callback_result)
while nma.still_scanning():
print('Waiting ..')
nma.wait(2) # you can do whatever you want but I choose to wait after the end of the scan
Homepage
http://xael.org/norman/python/python-nmap/
Changelog
2016/07/29 (v0.6.1)
- Fix bug #22 UnboundLocalError in scan_progressive
- Fix bug #23 Scanning fails on nmap warnings
- Fix bug #20: Fix for empty values which results in blank CSV output
- Fix bug #18: print(nm.csv()) does not return any results
- Fix bug #19: nmap program was not found in path
- Fix bug #17: hostname is no longer reported
2016/03/15 (v0.6.0)
- Add information about Nmap special licence
- Licence precision for distributing python-nmap along with nmap
2016/03/15 (v0.5.2)
- add hostname to csv export
2015/12/05 (v0.5.0-1)
- updating example.py
2015/11/18 (v0.5.0)
- Closes bugs :
- #11 Display only one osclass/osmatch instead of multiple
- Change in data structure :
- osmatch is a list of osclass
- osclass is a list of dictionnary
- added cpe which is a list of string
- added portused which is a list of dictionnary
Data structure for a host looks like :
```python
{'addresses': {'ipv4': '127.0.0.1'},
'hostnames': [],
'osmatch': [{'accuracy': '98',
'line': '36241',
'name': 'Juniper SA4000 SSL VPN gateway (IVE OS 7.0)',
'osclass': [{'accuracy': '98',
'cpe': ['cpe:/h:juniper:sa4000',
'cpe:/o:juniper:ive_os:7'],
'osfamily': 'IVE OS',
'osgen': '7.X',
'type': 'firewall',
'vendor': 'Juniper'}]},
{'accuracy': '91',
'line': '17374',
'name': 'Citrix Access Gateway VPN gateway',
'osclass': [{'accuracy': '91',
'cpe': [],
'osfamily': 'embedded',
'osgen': None,
'type': 'proxy server',
'vendor': 'Citrix'}]}],
'portused': [{'portid': '443', 'proto': 'tcp', 'state': 'open'},
{'portid': '113', 'proto': 'tcp', 'state': 'closed'}],
'status': {'reason': 'syn-ack', 'state': 'up'},
'tcp': {113: {'conf': '3',
'cpe': ',
'extrainfo': ',
'name': 'ident',
'product': ',
'reason': 'conn-refused',
'state': 'closed',
'version': '},
443: {'conf': '10',
'cpe': ',
'extrainfo': ',
'name': 'http',
'product': 'Juniper SA2000 or SA4000 VPN gateway http config',
'reason': 'syn-ack',
'state': 'open',
'version': '}},
'vendor': {}}
```
2015/11/17 (v0.4.7)
- Closes bugs :
- #10 Error when trying to parse 'osclass' , 'osmatch'
removed addresses, hostnames, status, vendor, osclass, uptime, osmatch
from all_protocols()
- Changed shebang line from python3 to python as it works with python2
2015/11/13 (v0.4.6)
- Closes bugs :
- #10 Error when trying to parse 'osclass' , 'osmatch'
2015/10/25 (v0.4.5)
- Closes bugs :
- #9 Can not pass ports with unicode string at scan function
2015/10/17 (v0.4.4)
- Closes bugs :
- #8 IPv6 Async scanner doesn't work
2015/09/11 (v0.4.3)
- Change in url for __get_last_online_version
2015/09/11 (v0.4.2)
- Closes bugs :
- #7: Error with empty hostname
- #6: Windows support of close_fds if you redirect stdin/stdout/stderr
2015/08/21 (v0.4.1)
- Closes bugs :
- #5: only one hostname stored per host
- Add hostnames() method which return the list of hostnames as a list of
dict [{'name':'hostname1', 'type':'PTR'}, {'name':'hostname2', 'type':'user'}]
2015/08/01 (v0.4.0)
- Closes bugs :
- #2: use close_fds in subprocess.Popen
- #3: memory leak parsing xml using xml.dom.minidom
- Corrects a bug in parsing osclass
- Add nosetests for case testing
- Removed test case in docstring
2015/05/08 (v0.3.7)
- adding sudo parameter for scanning (idea from scupython)
2015/05/08 (v0.3.6)
- correcting issue 7 : Issues under windows
2015/05/08 (v0.3.5)
- correcting a bug in all_protocols()
- correcting issue 8 : PortScannerAsync Doesn't work in windows..
2014/06/22 (v0.3.4)
- adding PortScannerYield class with generator
>>> nm = nmap.PortScannerYield()
>>> for i in nm.scan('127.0.0.1/24', '22-25'):
>>> print(i)
2014/03/13 (v0.3.3)
- moving file example.py
- adding function convert_nmap_output_to_encoding
- adding vendor for mac address
2013/09/23 (v0.3.2)
- adding acces to CPE values under [host][proto][port]['cpe'] key
2013/07/27 (v0.3.1)
- Bug correction on callback's assert in PortScannerAsync.scan
proposed by Robert Bost
2013/06/23 (v0.3.0)
- added support for NMAP SCRIPT ENGINE
>>> r=nm.scan(hosts='127.0.0.1', ports='139', arguments='-sC ')
>>> print(nm._scan_result['scan']['127.0.0.1']['hostscript'])
2013/02/24 (v0.2.7)
- added an address block in host scan result which contains ipv4, mac and other addresses :
nm = nmap.PortScanner()
r = nm.scan(arguments='-sS -p T:22', hosts='192.168.1.3')
print r['scan']['192.168.1.3']['addresses']
{u'mac': u'02:50:43:F4:02:B1', u'ipv4': u'192.168.1.3'}
- Adding a CSV scan output as a string.
- Changes examples.py to make it python3 compliant
2012/12/13 (v0.2.6)
- patch from lundberg.johan
- bug correction : when nmap doesn't work displays stderr instead of stdout
2012/11/23 (v0.2.5)
- corrected : Issue 2: 'map.nmap.PortScannerError: 'nmap program was not found in path' on CentOS
- corrected : Issue 3: nmap.scan() short-circuits prematurely
2011/11/09 (v0.2.4)
- implemented a request from Santhosh Edukulla :
parse OS scanning output
- Error with multiple host specifications :
bug and patch from old.schepperhand@gmail.com
2011/11/04
- bug in example.py : if no tcp port was open between 22-443
2010/12/17 (v0.2.3)
- adding __get_last_online_version to check if current version is the last published
2010/12/17 (v0.2.2)
- bug in handling nmap_error output (returned value was bin, string was expected)
- removed test strings form __init__.py file.
2010/12/15 (v0.2.1)
- corrected bug in __init__.py about scope problem
- try to find nmap executable in known directories
- raise AssertionError when trying to call command_line, scaninfo, scanstats, has_host before scanning
2010/12/14 (v0.2.0)
- Make python-nmap works with Python 3.x
- Contribution from Brian Bustin
2010/06/07 (v0.1.4)
- Patches from Steve 'Ashcrow' Milner
- remove shebang from __init__.py as it is not a runnable script
- allow use with ALPHA and BETA nmap releases
- .has_key() is deprecated, replaced instances with in
- move to using the print function for python2 and 3 usage
2010/06/04
- adding PortScanner.listscan
- PortScanner.scan now returns scan_result
- adding class PortScannerAsync (idea from Steve 'Ashcrow' Milner )
2010/06/03
- Import on google code
svn checkout https://python-nmap.googlecode.com/svn/trunk/ python-nmap --username XXXXX
- added PortScanner.scanstats method
- updated example.py and documentation for pingsweep
- updated Makefile for generating documentation
2010/03/09
- Modified packaging. v0.1.1 [norman]
2010/03/08
- Initial release. v0.1.0 [norman]
Release historyRelease notifications | RSS feed
0.6.1
0.6.0
0.5.0-1
0.5.0
0.4.7
0.4.6
0.4.4
0.4.3
0.4.2
0.4.1
0.4.0
0.3.7
0.3.6
0.3.5
0.3.4
0.3.3
0.3.1
0.2.7
Scan For Mac Address App
0.2.6
0.2.4
0.2.2
0.2.1
0.2.0
0.1.4
0.1.3
0.1.2
Nmap Scan For Mac Address
0.1.1
0.1.0
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
| Filename, size | File type | Python version | Upload date | Hashes |
|---|---|---|---|---|
| Filename, size python-nmap-0.6.1.tar.gz (42.0 kB) | File type Source | Python version None | Upload date | Hashes |
Nmap Get Mac Address
Hashes for python-nmap-0.6.1.tar.gz
| Algorithm | Hash digest |
|---|---|
| SHA256 | 80ba0eb10a52283a54a633f40b5baa9c2ff08675d6621dd089ead942852f5bd3 |
| MD5 | 2795bfcbc05cbbbccfcf4df59facaab1 |
| BLAKE2-256 | dcf29e1a2953d4d824e183ac033e3d223055e40e695fa6db2cb3e94a864eaa84 |
